Best .NET Obfuscators in 2026: An Honest Comparison
There is no shortage of .NET obfuscators. There is, however, a shortage of honest comparisons. Most "best obfuscator" lists are written by vendors, affiliates, or developers who evaluated one or two tools and stopped. This page covers every tool worth considering in 2026 - what each one actually does, what it costs, where it falls short, and which kind of project it suits best.
The tools covered: ArmDot, Dotfuscator Professional, Dotfuscator Community Edition, .NET Reactor, SmartAssembly, Eazfuscator.NET, ConfuserEx, and Obfuscar. Pricing and features are verified from official vendor sources as of early 2026.
Not sure what the threat actually looks like? .NET Decompilers Explained → shows exactly what ILSpy, dnSpy, and de4dot can recover from an unprotected assembly before you evaluate any tool.
What the comparison criteria actually mean
Before the table, it is worth being precise about what each criterion means in practice - because the marketing language around obfuscation is often vague.
Code virtualization is qualitatively different from all other obfuscation techniques. Where control flow obfuscation makes CIL harder to read, virtualization eliminates CIL entirely for selected methods and replaces it with a custom bytecode that runs on a proprietary VM embedded in the assembly. A decompiler looking at a virtualized method sees an interpreter loop, not your algorithm. It is the only technique that defeats both static and dynamic analysis simultaneously - at a performance cost of 10-20% on virtualized methods.
Cross-platform build support means the obfuscation tool itself - not just the protected output - can run on Linux and macOS. This matters for CI/CD pipelines. If your build agents run on Linux (common in cloud CI/CD for cost reasons) and your obfuscator only runs on Windows, you either need a Windows build agent or you skip protection in CI. That is a real operational constraint, not a theoretical one.
NuGet integration means the obfuscation step is declared inside the .csproj and runs automatically as part of dotnet build or dotnet publish. This is distinct from a tool that is installed on Windows and invoked manually or via a build script. With true NuGet integration, protection cannot be accidentally skipped.
Built-in licensing API means the tool includes functionality for serial key validation, hardware ID locking, and trial expiry for the software you are protecting - not licensing for the obfuscator itself. Only two tools in this comparison include this: ArmDot and .NET Reactor. For a detailed guide to implementing licensing with obfuscation, see the licensing protection guide →.
The comparison table
All prices are single developer licenses unless noted. "Perpetual" means a one-time purchase; the tool continues to work indefinitely but paid renewal is required for updates.
| ArmDot | Dotfuscator Pro | Dotfuscator CE | .NET Reactor | SmartAssembly | Eazfuscator.NET | ConfuserEx | Obfuscar | |
|---|---|---|---|---|---|---|---|---|
| Price | $499 | Contact for quote | Free (personal use) | $249 | ~$710/user/yr | $399 | Free (MIT) | Free (MIT) |
| License model | Perpetual + 1yr updates | Subscription | Free with VS | Perpetual + 1yr updates | Annual subscription | Perpetual + 1yr updates | Open source | Open source |
| Renewal cost | $250/yr | ~$4,250+/yr | N/A | ~$99/yr | Subscription | ~$99/yr | N/A | N/A |
| .NET 10 support | Yes | Unverified | Unverified | Yes | Yes | Yes | No | Yes |
| .NET 9 support | Yes | Yes (Sep 2025) | Unverified | Yes | Yes (Dec 2024) | Yes | No | Yes |
| .NET 8 support | Yes | Yes (Oct 2023) | Yes | Yes | Yes (Nov 2024) | Yes | No | Yes |
| Build on Linux/macOS | Yes | Yes (no GUI) | No | No | No | No | No | Yes |
| NuGet integration | Yes (full) | Yes (private pkg) | No | No | Yes | Yes (full) | No | Yes |
| Symbol renaming | Yes | Yes | Basic only | Yes | Yes | Yes | Yes | Yes |
| String encryption | Yes | Yes | No | Yes | Yes | Yes | Yes | XOR only |
| Control flow | Yes | Yes | Limited | Yes | Yes | Yes | Yes | No |
| Code virtualization | Yes | No | No | Yes | No | Yes | No | No |
| Anti-tamper | Yes (experimental) | Yes | Basic | Yes | Yes (Pro only) | No | Yes | No |
| Anti-debug | Implicit via VM | Yes | Basic | Yes | No | No | Yes | No |
| Resource encryption | Yes | No | No | Yes | No | Yes | No | No |
| App virtualization | Yes (Windows) | No | No | No | No | No | No | No |
| Built-in licensing | Yes | Expiry only | No | Yes (full) | No | No | No | No |
| Protects itself | Yes | Unknown | N/A | Unknown | Unknown | Unknown | N/A | N/A |
Tool-by-tool breakdown
ArmDot
ArmDot is the only tool in this comparison that is genuinely cross-platform for the build step - the obfuscator itself runs on Windows, Linux, and macOS, which means it works on any CI/CD runner without platform-specific configuration. It integrates via NuGet and MSBuild attributes written directly in source code, so protection is part of the build graph and cannot be skipped.
The standout feature is code virtualization. ArmDot generates a unique VM per build, meaning two protected builds of the same source produce different bytecode - there is no reusable analysis across builds. Anti-tamper is available but marked experimental. Anti-debug is not a dedicated feature; the resistance to dynamic analysis comes from virtualization making it very difficult to follow execution through the interpreter.
Beyond obfuscation, ArmDot includes a built-in licensing API with hardware ID locking, RSA-based serial key generation and validation, trial expiry enforcement, and integrity checking. This is the only tool other than .NET Reactor that combines obfuscation and licensing in a single product - and the only one where the licensing validation code is protected by the same virtualization that protects everything else. ArmDot also supports application virtualization (embedding any file, including unmanaged DLLs, into a single protected executable) - a Windows-only feature powered by BoxedApp technology.
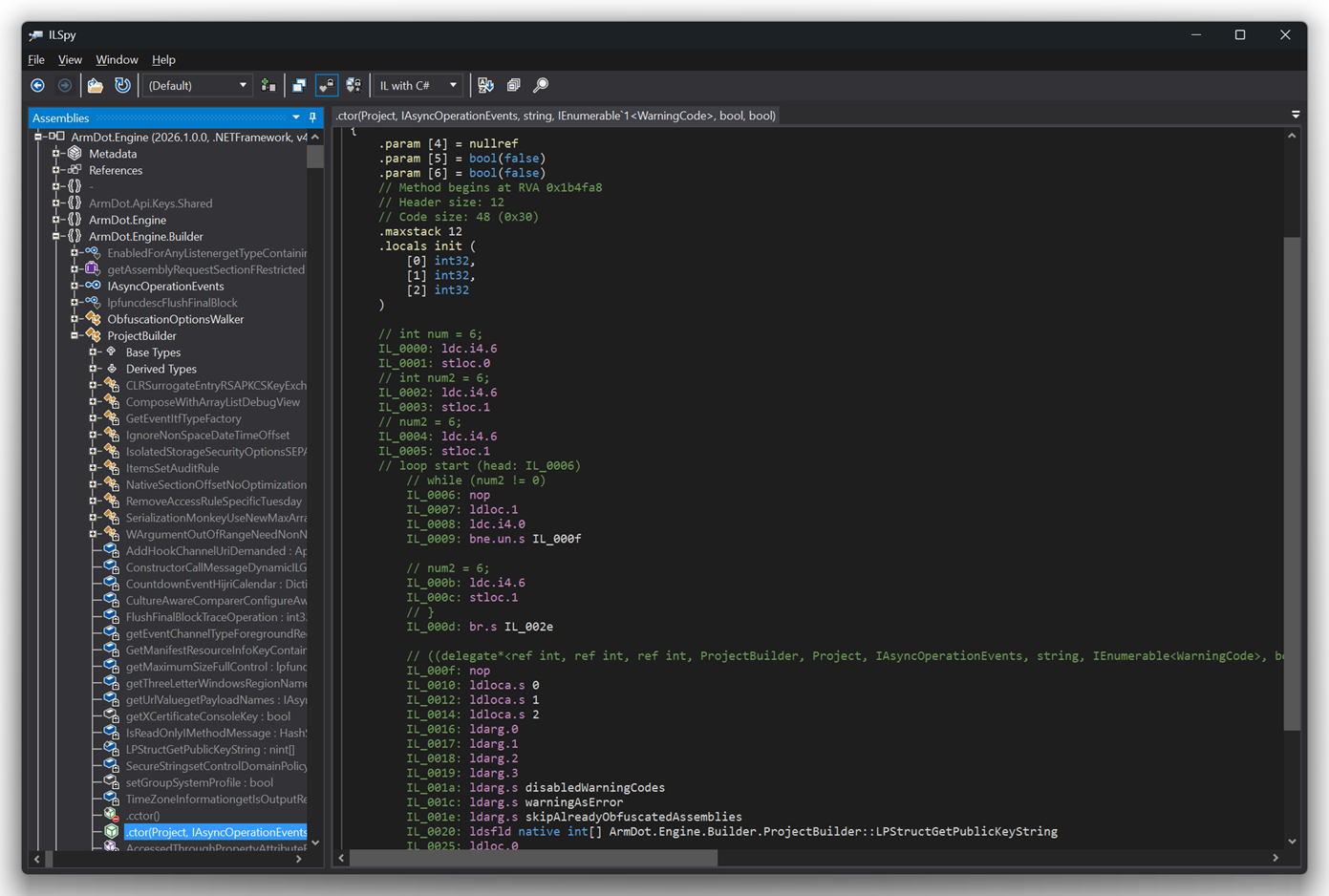
ArmDot's binaries are protected with ArmDot itself - you can verify this by opening the ArmDot executable in ILSpy.
Limitations: Anti-tamper is experimental. Anti-debug is implicit rather than explicit. Smaller community than .NET Reactor or Dotfuscator. Virtualization carries a significant performance overhead on compute-heavy methods - apply selectively to high-value methods, not entire assemblies.
Best for: ISVs shipping commercial desktop or server applications who need cross-platform CI/CD, code virtualization, and built-in licensing without buying separate products. Renewal at 50% of license price (~$250/year) makes the long-term cost predictable.
Dotfuscator Professional
Dotfuscator is the category's oldest commercial tool, having shipped with Visual Studio since .NET's early days. PreEmptive (now owned by Idera) targets enterprise teams - the language on their site is about Fortune 500 companies, compliance reporting, and RASP (Runtime Application Self-Protection) features that go beyond standard obfuscation.
Its patented Overload Induction renaming is genuinely sophisticated - it renames multiple methods to the same name, exploiting .NET's overloading rules to create additional confusion beyond simple token substitution. Anti-tamper and anti-debug are mature and configurable with custom response actions.
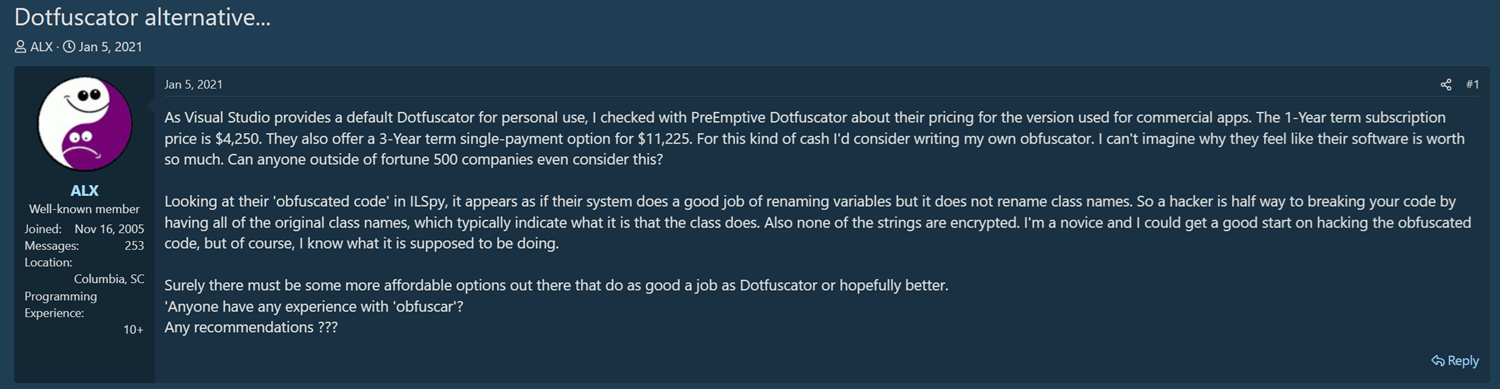
The pricing model is the most common reason developers look elsewhere. Pricing is not public - you need to contact sales. The last developer-reported figures were around $4,250 for a one-year subscription. NDepend publicly documented switching away from Dotfuscator after an 80% annual price increase over a decade of use.
The missing feature that surprises many evaluators: Dotfuscator Professional does not offer code virtualization. Despite being the most expensive tool in this comparison, the protection stack stops at control flow obfuscation. There is no built-in licensing API either - only a Shelf Life feature that bakes an expiration date into the assembly.
Limitations: No code virtualization. No licensing API. Pricing opaque and enterprise-tier. No Linux build agent support (NuGet package available but no GUI). .NET 9 support arrived in September 2025.
Best for: Enterprise teams with compliance requirements, existing Dotfuscator investments, or procurement processes where vendor support SLAs outweigh price considerations.
Dotfuscator Community Edition
Bundled with Visual Studio since .NET's earliest days. Personal and non-commercial use only - the license explicitly prohibits commercial distribution of software protected with CE.
Renaming is available but restricted to the basic Lower Alpha scheme. Library Mode is on by default, which means public types and members are not renamed. String encryption, assembly linking, incremental obfuscation, WPF/XAML renaming, and code virtualization are all Professional-only. Control flow obfuscation is present but limited.
Shelf Life (time-based expiry) is available in CE with registration, which is the one practical feature for developers testing trial protection.
Best for: Personal projects, learning, and evaluating Dotfuscator's workflow before committing to Professional.
.NET Reactor
.NET Reactor is the community's go-to recommendation for developers who want serious protection at a reasonable price. NDepend switched to it from Dotfuscator. It appears in more forum recommendations than any other paid obfuscator.
The feature set is the broadest in this comparison. NecroBit is .NET Reactor's proprietary IL code protection - it encrypts method bodies at rest and decrypts them on-demand at runtime, which is distinct from both standard control flow obfuscation and full virtualization. Code virtualization is also available, converting code to randomized VM instructions. The licensing API is full-featured: trial locks, hardware-locked licenses, time limits, and usage-based enforcement.
The limitation that matters most for modern development teams: the tool itself runs only on Windows. The CLI and GUI both require Windows. This means Linux and macOS build agents cannot run .NET Reactor directly. For teams with Windows build agents this is irrelevant; for teams running cloud CI/CD on Linux runners it is a genuine constraint.
The single developer license ($249) also excludes build server support - the company license ($549) is required for CI/CD use.
Limitations: Windows-only tool - no Linux or macOS build agent support. No dedicated NuGet build integration (standalone tool). Single developer license excludes CI/CD.
Best for: Windows-centric development teams that want the deepest feature set at the lowest price. The value proposition is strong for teams with Windows build infrastructure.
SmartAssembly
SmartAssembly is Redgate's .NET obfuscator, and Redgate is one of the most respected names in .NET tooling. The product's reputation was built on its unique Automated Error Reporting feature - SmartAssembly can inject exception capture, categorization, and reporting into your application without you writing any code. For teams that want combined protection and crash reporting in a single product, it is a genuine differentiator.
The .NET 8 support timeline is the most important fact about SmartAssembly for any team evaluating it today. .NET 8 shipped in November 2023. SmartAssembly did not support it until November 2024 - a twelve-month gap during which developers either could not upgrade their runtime or could not protect their builds. Community frustration during this period was significant and publicly documented on Redgate's support forums. The pace improved significantly for .NET 9 (December 2024, roughly one month after release) and .NET 10 (November 2025, same month as release).
SmartAssembly does not offer code virtualization. Anti-debug is not a documented feature. The tool itself runs on Windows only.
Limitations: No code virtualization. No anti-debug. No licensing API. Windows-only tool. Historical .NET version support delays (though improved recently). Annual subscription model.
Best for: Teams that value Redgate's support quality and specifically need automated error reporting alongside obfuscation.
Eazfuscator.NET
Eazfuscator.NET from Gapotchenko deserves more attention than it typically receives. Its NuGet integration is the smoothest of any tool in this comparison - install the Gapotchenko.Eazfuscator.NET package, and every Release build is automatically protected. No separate configuration file, no build script changes.
The feature set is strong: renaming, string encryption, control flow, and code virtualization with a custom VM that generates a different virtual instruction set on each obfuscation run. It also claims to be the first commercial obfuscator to implement homomorphic encryption - a technique that allows computation on encrypted values without decrypting them first.
The single developer license at $399 limits usage to 16 CPU cores. Anti-tamper and anti-debug are not listed as discrete features - resistance to dynamic analysis comes from virtualization rather than dedicated detection routines. No licensing API.
Limitations: No anti-tamper or anti-debug as dedicated features. No licensing API. Windows-only tool. CPU core limit on single developer license.
Best for: Developers who want the smoothest possible NuGet-first obfuscation workflow with code virtualization, without needing licensing functionality.
ConfuserEx
ConfuserEx was archived on GitHub in January 2019. The last release was v1.0.0 in July 2016. It does not support .NET 5, 6, 7, 8, 9, or 10. The community fork mkaring/ConfuserEx extends support to .NET Framework 4.8 but does not resolve the modern .NET incompatibility.
For .NET Framework 4.x projects with no plans to migrate, ConfuserEx works. For anything targeting modern .NET, it does not. There is also a dedicated de4dot fork (de4dot-cex) that handles deobfuscation of ConfuserEx-protected assemblies, which means the protection it offered in 2016 is now significantly weaker against motivated attackers.
See: ConfuserEx Alternatives for Modern .NET →
Obfuscar
Obfuscar is an actively maintained open-source obfuscator with over 2.6 million combined NuGet downloads. It supports modern .NET including .NET 10 (added in v2.2.49), runs cross-platform, and integrates via NuGet GlobalTool.
What it does not do: control flow obfuscation, code virtualization, anti-tamper, anti-debug, or meaningful string protection (its string hiding uses reversible XOR encoding - the official documentation explicitly warns against using it for sensitive strings). It is a renaming tool with limited supplementary features.
A v3.0 rewrite (currently in beta) replaces Mono.Cecil with System.Reflection.Metadata for significant performance improvements, but does not add protection techniques.
Best for: Open-source projects or commercial projects where basic renaming is the only requirement and budget is zero.
Which tool is right for you?
ISV shipping commercial desktop or server software - ArmDot. Cross-platform builds, NuGet integration, code virtualization, and a built-in licensing system in one product. The perpetual license at $499 with ~$250/year renewal is the most predictable long-term cost in this category.
Budget-constrained independent developer - .NET Reactor at $249 is the honest answer. The deepest feature set per dollar in the market, including code virtualization and a full licensing API. The Windows-only constraint matters less if you are already developing on Windows.
Enterprise team with compliance requirements - Dotfuscator Professional or SmartAssembly. Both have larger support organizations, audit trail capabilities, and established enterprise track records. Get a Dotfuscator quote before committing; the pricing may or may not be acceptable depending on your budget.
Unity game developer - see our dedicated Unity C# obfuscation guide → for the specific constraints of IL2CPP and Mono targets.
Team that wants the simplest possible NuGet workflow - Eazfuscator.NET. Install the package, build in Release, done. Code virtualization included.
Developer on .NET Framework 4.x only, zero budget - ConfuserEx still works for this narrow case, though its protections are increasingly well-understood by attackers.
Open source project needing basic renaming - Obfuscar. Free, cross-platform, actively maintained.
See also:
- Dotfuscator Alternative: Why Developers Are Switching →
- ConfuserEx Alternative for Modern .NET →
- Free vs Paid .NET Obfuscators: An Honest Assessment →
- .NET Decompilers Explained →
Back to: .NET Obfuscation: The Complete Developer Guide →
Protect your .NET application with ArmDot
ArmDot is available with a free trial - assemblies protected during evaluation stop working after two weeks, giving you time to test the full workflow. A single developer license is $499, includes one year of upgrades, and covers Windows, Linux, and macOS builds.
